 Perhaps it is telling that my first post of the year is one dealing with recent articles on cybersecurity. Perhaps it is a recognition that 2018 may be the year when cybersecurity come even more to the fore, both from the protection of our personal systems, to the protection of our voting systems, and to the tampering that occurs in our systems. But it may also be reflective of the fear, uncertainty, and distrust that is growing in our society today, where every risk is super scary. Part of the problem is that people either confuse or don’t understand the terms. So, let’s be clear (and these are from NIST SP 800-37 Rev 1):
Perhaps it is telling that my first post of the year is one dealing with recent articles on cybersecurity. Perhaps it is a recognition that 2018 may be the year when cybersecurity come even more to the fore, both from the protection of our personal systems, to the protection of our voting systems, and to the tampering that occurs in our systems. But it may also be reflective of the fear, uncertainty, and distrust that is growing in our society today, where every risk is super scary. Part of the problem is that people either confuse or don’t understand the terms. So, let’s be clear (and these are from NIST SP 800-37 Rev 1):
- Risk [FIPS 200, Adapted]. A measure of the extent to which an entity is threatened by a potential circumstance or event, and typically a function of: (i) the adverse impacts that would arise if the circumstance or event occurs; and (ii) the likelihood of occurrence.
- Threat [CNSSI 4009, Adapted]. Any circumstance or event with the potential to adversely impact organizational operations (including mission, functions, image, or reputation), organizational assets, individuals, other organizations, or the Nation through an information system via unauthorized access, destruction, disclosure, modification of information, and/or denial of service.
- Vulnerability [CNSSI 4009]. Weakness in an information system, system security procedures, internal controls, or implementation that could be exploited or triggered by a threat source.
There is no such thing as a “mega-vulnerability”. “Mega” is a risk assessment, and requires not only the weakness from the vulnerability, but a high likelihood of exploitation by a likely threat, and a likely adverse impact of that exploitation. You can have a vulnerability in a system that is easy to exploit, but doesn’t get you much information. You can have one that is hard to exploit, but can get you a lot of information. Risk depends not only on the vulnerability and the likelihood of exploitation, but the context of use and the likely attackers (threats), in order to determine the overall risk.
With that, let’s look at some news:
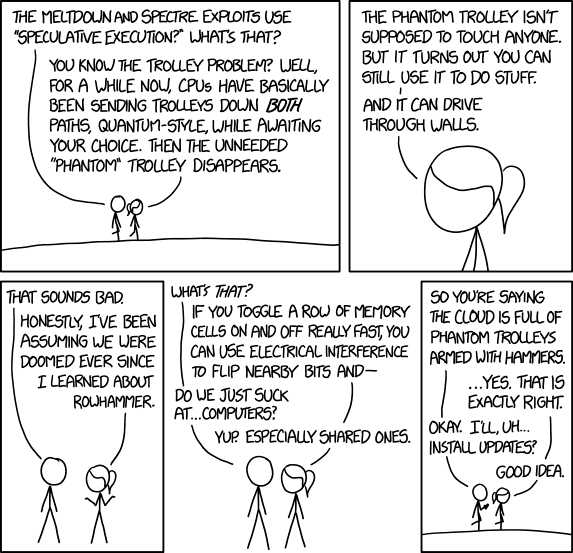
- Meltdown and Spectre. You’ve heard about these (makes air quotes) mega-vulnerabilities (end air quotes). They can impact almost any processor that does predictive execution. That includes Intel, AMD, and ARM processors. They can look into memory and expose data. Fixing them will slow down your system. There are emergency Windows updates being issued for Windows 10. But beyond the fear, what do you know? What is the risk? Here are the gory details on the problem. If you read through this, you’ll see that these aren’t they easy to exploit. You need to get someone to run a specially crafted program, and it needs to be on a system that might have some information you need. For most people, the risk from this is low. That doesn’t mean you don’t want to patch it as soon as you can — the longer a vulnerability is out there, the more it will be exploited. But this isn’t the world coming to an end. It does, however, demonstrate a few key rules: (1) complexity is your enemy — the larger and more complex a system it, the more likely that there will be undiscovered vulnerabilities; (2) because it is hardware/on a chip, doesn’t mean it is secure — we make the assumption that because something isn’t obviously software, that it isn’t security. But today’s firmware can be equally complex, and the hardware circuit designs even more so, just being on a chip doesn’t make it secure.
- Edited to add: Here’s some additional “late breaking” links: (1) all Apple devices are affected; (2) Google has a browser fix for Spectre, with negligible impact (as well as additional details on the attack); (3) Hacker News has an overall guide on how to protect your devices; (4) In a similar vein: how to protect your PC; and (5) Intel reacted about the same way when the F00F bug attacked 20 years ago. Oh, and there’s a new critical flaw in Western Digital “My Cloud” storage devices. Complexity, my friends, complexity. And people wonder why I use a single purpose iPod Classic to play my music, instead of my phone.
- Edited to add (from the ever excellent XKCD):
- Secure Your Router. Whereas Meltdown might be lower risk, here’s a greater risk — and one that you likely can’t do much about: Your router. You need to secure your home router. Absolutely, positively. This is the router that connects your ISP to your home systems. You need to (at minimum) change the administrator passwords, set up the appropriate NAT, and ideally use a DNS other than your ISP’s DNS. You also need to update the firmware regularly, although you might not be able to do that. If you can’t, you need to consider that router a compromise zone, and put something more secure behind it for your use. Let the guest’s you don’t care about use the ISP’s wireless.
- Ransomware. An emerging trend (unfortunately) is ransomware. Ransomware doesn’t steal your data; rather, it demands money so you can access it. It is insidious and evil, and far too easy to run into with all the hidden drive-by-downloads. So bookmark the following site: No More Ransomware. It is a clearinghouse of information on how to remove ransomware infections.
- Attacking Hard Disks. Meltdown and Spectre can only get to information in memory. What about your hard disk? What about an attack that could cause the disk to crash? What if that attack didn’t require you to get on the system at all? Scared? Such an attack exists: Gizmodo is reporting on attacks using sound to crash hard disks by exploiting resonant frequencies.
- Voting Machines. Of course, it isn’t just home machines and businesses that get attacked. Our voting systems get attacked, as we saw in the 2016 elections. But just as a broken clock tells the right time twice a day, the GOP-led Congress actually has a reasonable bill proposal regarding secure voting. Learn about this bill, and if you agree with its approach, work to secure its passage. The bill creates earmarks to help states get rid of their paperless electronic voting machine in favor of voter-verified, machine-readable paper ballots, and institutes a system of randomized post-election audits that use good statistical techniques to spot systemic anomalies. This may become even more important as states move away from precincts and to voting centers.
- Edited to add: I pointed out the above to a friend who is very concerned about cybersecurity and elections, and she had this response — which I think highlights something important: “The congressional initiative on secure voting does advance the use of paper, but it does nothing to end the imposition of vulnerable expensive private architecture on public record management. In fact it serves to continue it. “Trusting” states to hire impartial auditors and to conduct audits is a stretch. A sponsor, Kamala Harris’s lack of discernment has so far been a big disappointment. First Franken. Now this.”

